|
16 ALPHANUMERIC ENCODED KEY WEARABLE KEYGLOVE Rhyan Andrade, Allan De Jesus, Tristan Calasanz, Carlos Oppus, and Dr. Rosula Reyes Abstract - A key glove provides an alternative and portable input device for wearable computing. As research on wearable technology increases, the design of an unobtrusive and portable input device becomes invaluable. This project aims to provide inputs similar to the keys of a keyboard. However, unlike the keyboard, the keys are directly fitted on the glove. Furthermore, the key glove utilizes an interface similar to that of cell phones where several keys are encoded in a single contact. This reduces most of the keys of a 101-key keyboard into 11 contacts only. Thus, this improves the ergonomics of the keyer and makes it easier for the user to learn the configuration. Such a design allows the user to perform multiple tasks and to achieve portability and convenience. I. INTRODUCTIONWearable computing facilitates a synergy of physical reality and augmented reality, which enables the human to freely interact with his/her computer in any environment. This means that the computer is "always on" and "always ready" for the human to access. This facilitates the gathering of on the fly information within reach. With the advent of small and powerful computers, the development of wearable computing is ever more plausible. A wearable computer then is a computer that is subsumed into the personal space of the user, controlled by the user, and has both operational and interactional constancy, i.e. is always on and always accessible. In essence, there are six attributes that characterize a wearable computer. First, it is unmonopolizing of the user’s attention in a way that does not cut off the user from the outside world. It is built with the assumption that computing will be a secondary activity rather than a primary focus of attention. Second, a wearable computer should not be restricting to the user. It should be ambulatory, mobile, and roving, which means that it would allow the user to do other things while using it. Third, its output medium must be constantly perceptible or observable to the user. Fourth, the computer should be entirely controllable by the user. The controls should be responsive which would allow the user to grab control of the computer any time that he/she wishes. Fifth, it can also be attentive to the environment, being environmentally aware, multimodal, and multisensory. Ultimately, it could give the user increased situational awareness. Finally, the wearable computer should be communicative to others. In other words, it can be used as a communications medium. At the same time, it should also allow the user to be expressive through the medium. A key glove is an input device for wearable computing that supports several of these attributes. Being an input device, it gives the user responsive control over the computer and at the same time, it also serves as a communications medium. Furthermore, because of its characteristic design for portability, it is not restricting to the user. It still allows the user to do other activities while entering commands to the computer through keypresses. II. STATEMENT OF THE PROBLEMAt present, personal computers sit on the desk and interact with the users for only a small fraction of the day. Their capability for information access and data management is not fully realized for most of the time. Hence, a person’s computer should be worn and interact with the user based on the context of the situation. With heads-up displays, unobtrusive input devices, personal wireless local area networks, and a host of other context sensing and communication tools, the wearable computer should act as an intelligent assistant that could access, process, and store information anytime and anywhere the user wants. As such, the design of an alternative and portable input device such as a key glove is a fine research for the development of wearable computing. Ideally, it should be able to incorporate all the keyboard functions into one small input device to achieve absolute portability. Along with this, the device should not have any external power supply since this would make the design hulky. However, the ergonomics of such a design should also be considered so that the ease of its usage would not be sacrificed. Users must find the device convenient to use.
The main task of this study is to create a user interface that would duplicate that of a normal A/T or PS2 keyboard. Thus the project aims at the following objectives. Figure 1: A/T and PS2 plugs
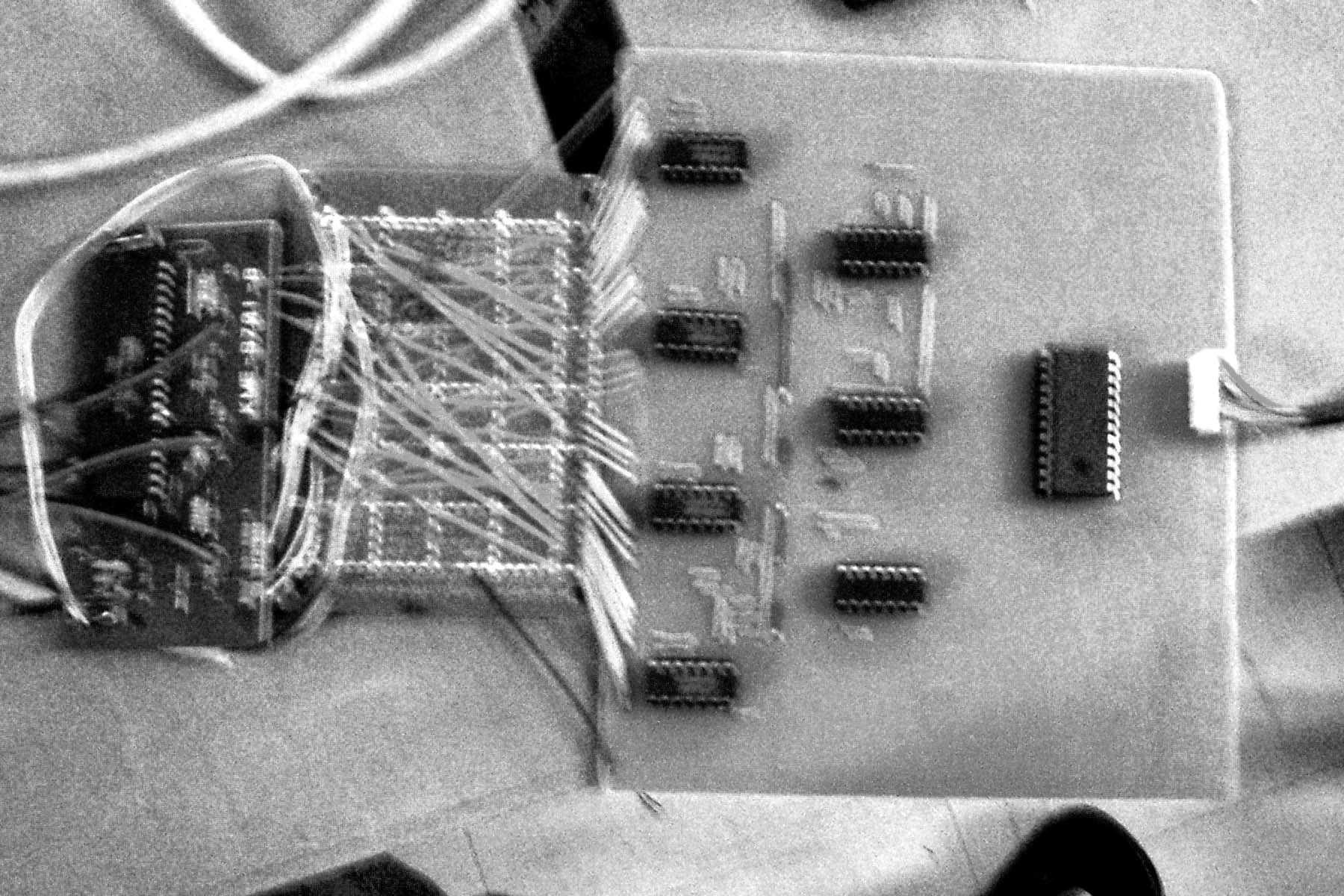
After realizing the different issues for the project, the proponents decided to implement the following methods: 1. Hardware implementation: Since the keyboard industry has developed a stable and dependable input device, it was decided that the prevailing layer be used as the base layer. In doing so, the main interest of the hardware component is how to link the 16-key key glove to a standard keyboard controller. To do this, prevailing technologies were once again consulted and a 16-key keyboard encoder was obtained. The use of this IC had effectively reduced the number of wires that could obstruct the user from fulfilling his tasks. Furthermore, bilateral electronic switches (4066) were used to duplicate the shorting of the two nodes in the keyboard matrix. In so doing, the key glove was linked to the normal A/T keyboard controller. Furthermore, since no active components were used, it was safe enough to draw the power from the 5-volt signal of the A/T / PS2 port and thus, no longer need any opto-isolator circuit. Figure 2: Keyglove w/ 16 key-keyboard encoder
Figure 3: Layout of the Printed circuit board
2. Software Implementation The other part of the project is the software, which handles the routine for encoding a particular key through multiple "keypresses" similar to that of the cell phone. To do this, the routine accesses the keyboard buffers by calling the interrupt 16 handler of DOS. Afterwards, the scan codes and character codes were obtained to identify which key was pressed. From there, by implementing a simple counter and subjecting it to a time limit, the original input code was replaced with a different one depending on the current value of the counter. This new code would be the one echoed in the application.
This project tried implementing the 101 keys of a standard keyboard into the 16 keys of the glove. Although possible, the proponents encountered difficulties in doing so while considering the ergonomics of the design. As such, only 45 functions of the standard keyboard were implemented which were mainly alphanumeric characters. Figure 4: Layout of the contacts in the Keyglove
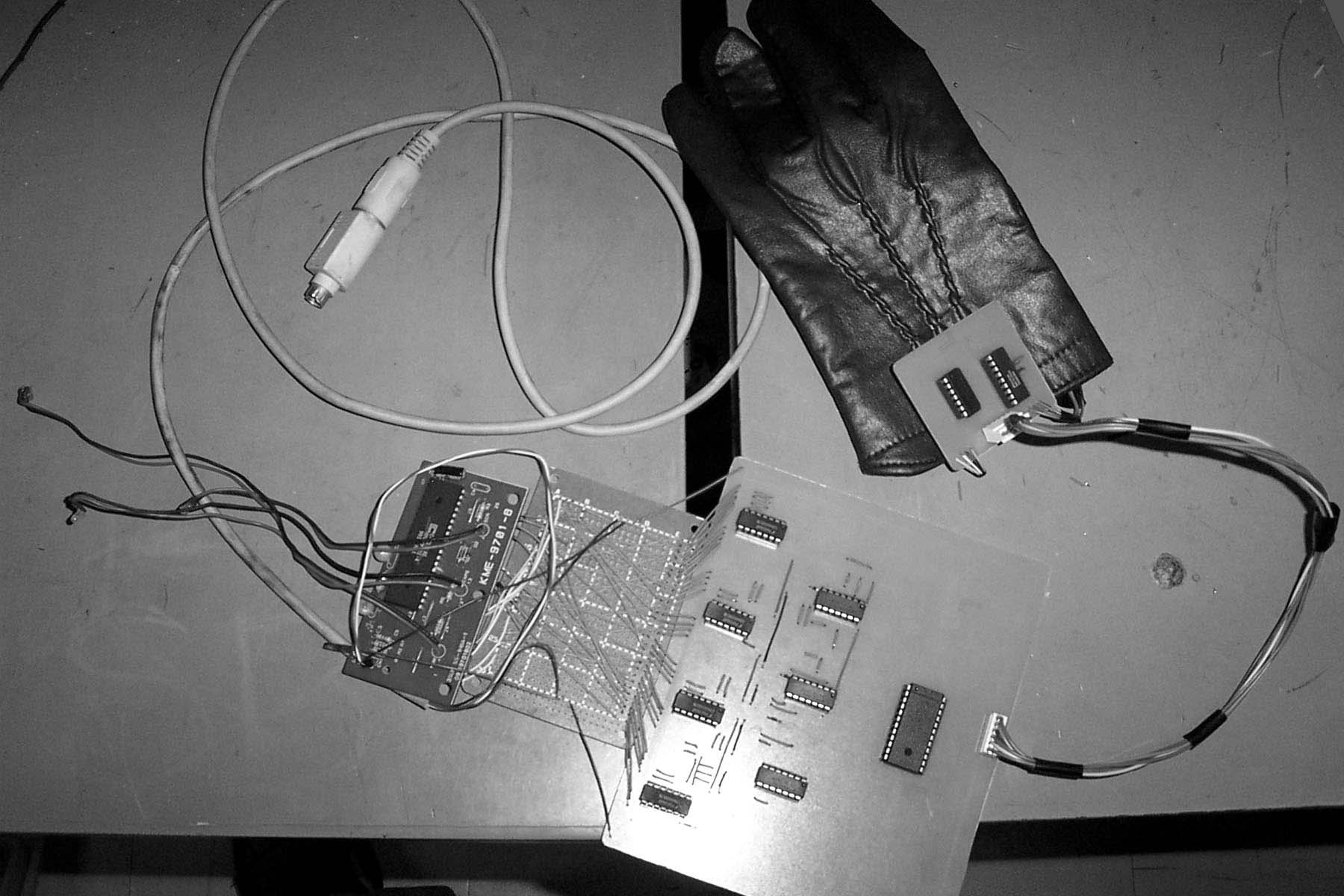
Another limitation of the hardware was the use of an older version of the keyboard controller. Thus, the hardware became processor dependent since it is not capable of handling the higher clock speeds of advanced processors. Figure 5: Keyglove project
The proponents were also limited in their knowledge in system programming. It was intended that the program would allow the inputs from the key glove to be used in any application in either DOS or Windows. Therefore, the prototype presently runs only in its own environment. III. HARDWARE SETUP AND CONFIGURATIONThe primary objective of the hardware part of the project is to directly interface the designed key glove into a computer. The key glove consists of a leather glove with 11 metal contacts sewn straight on the material. These contacts are then connected to a 16-key encoder. They are interpreted as rows and columns, which are presented in the following block diagram.
The purpose of the 16-key encoder is to reduce the number of wires connecting from the glove to the computer. Any connection between a row and a column would then be encoded into a 4-bit output. Each specific encoded output would represent a particular key. The table given below shows the key character assigned and its corresponding output under a specific pair of rows and columns. Note that there is no key assigned for the pair C4 and R4. The 4x16 decoder is a TTL device such that if it has no input, it would only send a logic low in its 16th bit output. In other words, if no contact is connected with another, the prototype would always send the key assigned for the 16th bit output.
This 4-bit output would now pass through a 4x16 decoder as shown in the diagram directly above. Remember that the output of the decoder is an active low enable. Thus, to send a high signal from the output, the output from the decoder must pass through inverters. These outputs in turn would enable the nodes in the 4066 electronic switches at a logic high. One electronic switch is connected to one pair of pins in the keyboard controller. If any of these pairs is shorted due to a high enable, the controller would send a hardware interrupt along with a particular scan code and a character code corresponding to the pair shorted to the computer. IV. SOFTWARE SETUP AND CONFIGURATIONIn implementing the software, the routine performs the following actions: From this flowchart , we can see that we are primarily concerned with the keyboard buffer. We need to access the keyboard buffer: one to know when and what key was pressed and two, to put it again in buffer to be past on the next application that will call int 16. Fortunately, C++, has a simple way of accessing the keyboard buffer by using the dos.h header file. In the dos.h header, there is a function called int86() in which by placing the right hexadecimal number on the regs.h.ah register, you are able to call a particular function of an interrupt. Included in the parameters are the intterupt to be called input registers and output registers. From this, we can easily catch key presses and subject those values to comparisons so that we can indeed determine the output for the "key-in". Below is an example of the code used: while (keyin!='+') { regs.h.ah = 0x0; int86(0x16, ®s, ®s); keyin= regs.h.al; counter = 1; .... asm push ax; asm push dx; asm mov ah,02h; asm mov dl,08h; asm int 21h; asm pop dx; asm pop ax; .. V. CONCLUSION
Presently, research is being done on wearable technology in different countries. It would then be a matter of time before wearable computing becomes a trend in the field of information technology. The world cannot deny its value and significance considering that a wearable computer is a portable data processor, which can be accessed by any user any time and any place. Its utility could permeate in every aspect of human life. A wearable computer is composed of several parts, which are similar to that of a personal computer. One such component is the keyglove that serves as an input device for the machine. Like any wearable, the keyglove can be worn on the person and can be brought anywhere. Thus, it achieves absolute portability while at the same time serve as a standard keyboard. The project had moved towards this absolute portability. It still managed to implement the most common functions of a standard keyboard given that the project had several limitations. Although the ergonomics of the design limited the number of physical "keys" to 16, the use of a software that emulates the key press routine of a cellular phone had expanded this to as much as 45 key functions. Note that the eleven contacts of the glove are arranged in a way that makes use of the flexibility of all five fingers but does not necessarily strain the muscles. Ultimately, the strength of the project lies in its capability to scale down a bulky input device such as the keyboard into something wearable such as the keyglove that does not restrict the user and at the same time still possessing the important functions of its predecessor. REFERENCES
|